Better ‘Cyber Hygiene Among Small Businesses
The proportion of businesses in the UK reporting cyber attacks and data…
Payment Fraud Detection and Prevention: Here’s All To Know
Key takeaways: With AI technology, payment fraud and fraud prevention have become…
Google Chrome Update Fixes Zero-Day Security Flaw That Targeted Media, Government and Educational Institutions
Google has fixed a serious security vulnerability affecting its Google Chrome browser,…
Google Chrome Update Fixes Zero-Day Security Flaw That Targeted Media, Government and Educational Institutions
Google has fixed a serious security vulnerability affecting its Google Chrome browser,…
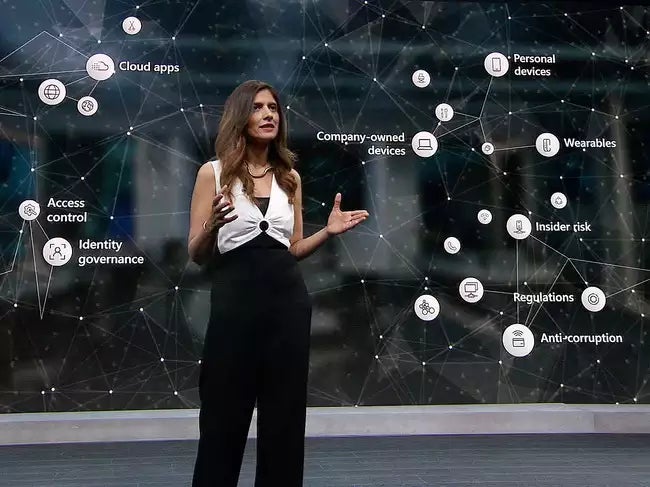
Microsoft Adds Even More AI to Its Security Copilot
Vasu Jakkal, corporate vice president, Microsoft Security. Image: Microsoft Microsoft is raising…
Apple Passwords App Vulnerability Exposed Users for Months
Apple’s Passwords app, designed to enhance security for iOS users, ironically left…
FBI & CISA Urge Immediate Action
Image: DC_Studio/Envato Elements Federal cybersecurity officials are raising red flags over a…
How to Prevent Phishing Attacks with Multi-Factor Authentication
Phishing takes advantage of the weakest link in any organization’s cybersecurity system…
Sneaky Log Phishing Scheme Targets Two-Factor Security
Security researchers at French firm Sekoia detected a new phishing-as-a-service kit targeting…
Protect 3 Devices With This Maximum Security Software
TL;DR: Protect your privacy on three devices with a 1-year subscription to…